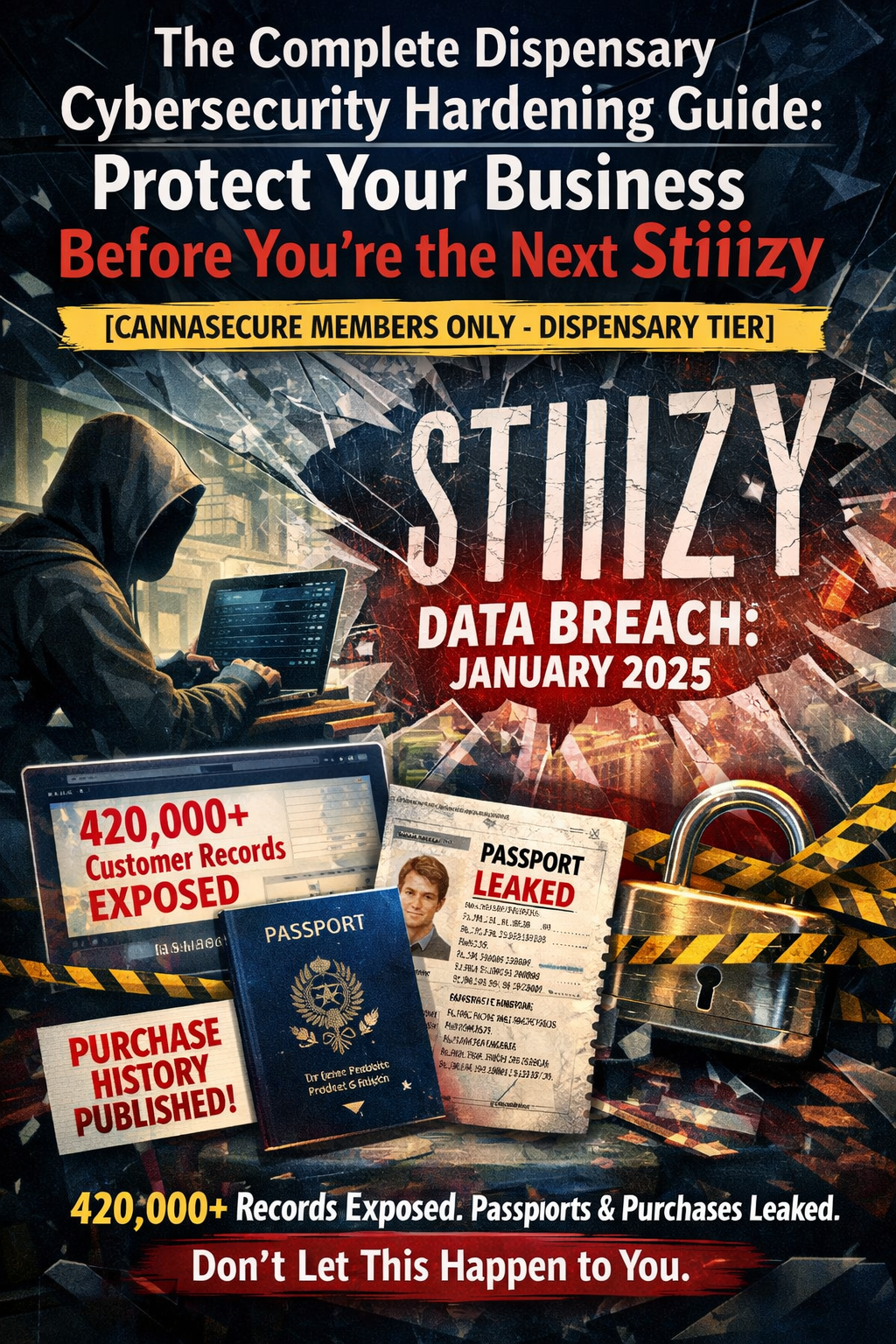
The $380,000 Wake-Up Call
In November 2024, STIIIZY—one of California’s largest cannabis retailers—sent breach notifications to 380,000 customers. Names, addresses, birth dates, driver’s license numbers, and medical cannabis card details were exposed through a compromised point-of-sale system.
This wasn’t an isolated incident. It was the latest in a growing pattern of attacks targeting an industry uniquely vulnerable to cyber threats.
The cannabis industry operates at the intersection of multiple risk factors: it’s cash-heavy, data-rich, heavily regulated, and often lacks mature cybersecurity infrastructure. For cybercriminals, dispensaries are high-value targets with lower defenses than traditional retail.
If you’re operating a dispensary, cultivation facility, or any cannabis business in 2026, cybersecurity isn’t optional anymore. It’s survival.
Why Cannabis Businesses Are Prime Targets
1. You’re Holding Gold
Cannabis businesses collect and store exceptionally valuable data:
- Customer identities: Government IDs, medical cards, addresses
- Purchase histories: Detailed records of consumption patterns
- Health information: Medical conditions, physician recommendations (HIPAA-protected)
- Financial records: Cash flow data, banking details, employee information
For medical dispensaries, you’re essentially operating a pharmacy without the cybersecurity budget of CVS or Walgreens.
2. You’re New to This
According to cybersecurity research, 43% of cyberattacks target small and medium-sized businesses. Most cannabis operations fall into this category.
The industry is relatively new, meaning:
- Many businesses are in startup phase, focused on compliance and growth over security
- There’s limited institutional knowledge about cannabis-specific cyber threats
- Most operations lack dedicated IT staff or security professionals
- Best practices are still emerging
3. You’re Operating in a Gray Zone
Federal restrictions create unique vulnerabilities:
- Major credit card networks won’t process cannabis transactions
- You’re forced to use alternative payment systems like “cashless ATMs”
- These workarounds introduce additional security gaps
- Limited banking access means limited access to enterprise-grade financial security
4. Privacy Matters More
Despite legalization progress, cannabis use still carries stigma. A data breach at a dispensary isn’t just inconvenient—it can expose patients’ medical conditions and consumption habits.
High-profile customers (executives, athletes, entertainers) are particularly vulnerable. This makes your customer data more valuable to extortionists and more damaging when leaked.
The Major Threat Landscape for 2026
Ransomware Attacks
Ransomware remains the nuclear option for cannabis cybercriminals.
How it works: Attackers encrypt your critical systems and demand cryptocurrency payment to restore access. Your point-of-sale system, inventory tracking, security cameras, compliance records—all locked.
Recent example: The average ransomware incident now costs $4.6 million, and cases are increasing year-over-year in high-risk industries.
Why you’re vulnerable: Many dispensaries run on Windows-based POS systems with outdated security patches. Staff members click phishing emails. Backups aren’t isolated from the network.
Impact: Complete operational shutdown. You can’t process transactions, track inventory for compliance, or access customer records. Every hour of downtime costs revenue and risks regulatory violations.
Point-of-Sale (POS) Compromises
Your POS system is patient zero for most cannabis cyberattacks.
The STIIIZY breach happened because their POS vendor’s system was compromised. When third-party systems are breached, all connected dispensaries get infected.
What attackers steal:
- Credit card data (for cashless ATM transactions)
- Customer credentials and personal information
- Transaction histories
- Employee login credentials
Why POS systems fail:
- Cloud-based systems with weak authentication
- Vendors without dedicated security teams
- Integration vulnerabilities with inventory and compliance software
- Limited security auditing of third-party providers
Third-Party Vendor Breaches
The cannabis industry runs on specialized vendors:
- Seed-to-sale tracking (Metrc, BioTrack)
- Compliance software
- Payment processors
- Customer loyalty platforms
- Inventory management systems
Each integration is a potential attack vector.
MJ Freeway experienced repeated breaches that disrupted dispensary operations across multiple states. The software—required by many states for regulatory compliance—became a liability when attackers infiltrated it.
The 2020 cannabis software breach impacted 30,000 customers across multiple U.S. dispensaries through a single vendor compromise.
You can have perfect internal security and still get breached through a vendor with weak protocols.
Phishing & Social Engineering
Phishing remains the #1 initial attack vector because it targets the weakest link: humans.
Cannabis-specific phishing tactics:
- Fake compliance emails: “Your Metrc account needs immediate verification”
- Banking access scams: “Your cashless ATM provider needs updated information”
- Regulatory urgency: “New state cannabis regulations require account verification”
- Holiday/event timing: Attacks spike around 420, harvest seasons, and major cannabis policy news
Why it works: Your staff is busy, compliance deadlines are real, and the consequences of missing regulatory requirements are severe. Attackers exploit this urgency.
Insider Threats
Cannabis businesses face high employee turnover. Every departing employee represents a potential security risk.
Risks include:
- Unauthorized access to customer databases
- Theft of proprietary cultivation methods or recipes
- Exposure of financial records
- Sabotage of inventory systems
The 2017 delivery service breach: A former employee of a medical referral agency stole data and demanded $70 million in ransom.
Supply Chain Attacks
Your digital supply chain includes growers, processors, distributors, and retailers—all connected through inventory tracking and compliance systems.
Attackers target the vendor with the weakest security to access the entire network. If your cultivation partner gets breached, their compromise can spread to your systems through shared platforms.
Real-World Cannabis Breach Timeline
Understanding the history helps prevent the future:
2017: MJ Freeway hacked twice in one year, disrupting compliance tracking 2018: Washington state’s cannabis database cyber incident, 5,000+ customer records stolen 2018: Ontario Cannabis Store breach, 5,000 customers compromised 2018-2019: Alberta medical referral agency attacked, health records accessed 2020: Cannabis software company breach impacts 30,000 customers across multiple dispensaries 2024: STIIIZY breach exposes 380,000 customer records 2025: Trulieve ransomware attack compromises customer data, enhances security protocols post-breach
Pattern recognition: Breaches are increasing in frequency and scale. The attackers are getting more sophisticated. The industry is growing faster than its security maturity.
The True Cost of a Cannabis Data Breach
Direct Financial Impact
- Ransom payments (typically demanded in cryptocurrency)
- Legal fees and regulatory fines
- Forensic investigation costs
- Credit monitoring services for affected customers
- System restoration and security upgrades
Operational Disruption
- Days or weeks of system downtime
- Lost revenue from halted transactions
- Compliance reporting delays (potentially triggering regulatory action)
- Productivity loss during recovery
Reputational Damage
- 87% of customers are less likely to do business with a company after a data breach
- Medical patients lose trust in your privacy protections
- Negative media coverage in local and cannabis industry press
- Competitive disadvantage as customers switch to “more secure” competitors
Regulatory Consequences
- State cannabis regulators may investigate your security practices
- Potential license suspension or additional compliance requirements
- HIPAA violations for medical dispensaries (up to $50,000 per violation)
Long-Term Business Impact
- Increased insurance premiums
- Loss of payment processing capability (catastrophic for cash-limited businesses)
- Difficulty attracting investors or selling the business
- 60% of small businesses close within 6 months of a major breach
Essential Security Measures for 2026
1. Employee Training (Your First Line of Defense)
Your staff is both your greatest vulnerability and your strongest protection.
Implement quarterly security training covering:
- How to recognize phishing emails (especially cannabis-specific tactics)
- Password security and credential management
- Physical security protocols for computers and terminals
- Incident reporting procedures
- Social engineering awareness
Create a security culture: Make it easy for employees to report suspicious emails. Set up a dedicated Slack channel or email for sharing potential phishing attempts.
2. Strong Authentication
Multi-factor authentication (MFA) is non-negotiable in 2026.
Implement MFA for:
- POS systems
- Email accounts
- Compliance software (Metrc, BioTrack, etc.)
- Customer databases
- Financial systems
- Remote access tools
Not all MFA is equal: Avoid SMS-based authentication (vulnerable to SIM-swapping). Use authenticator apps or hardware keys.
3. Vendor Security Assessments
Before integrating any third-party system, ask:
- Do they have a dedicated security team?
- When was their last security audit or penetration test?
- What certifications do they hold? (SOC 2, ISO 27001)
- What’s their incident response plan?
- Have they experienced breaches? How did they respond?
- Do they carry cyber liability insurance?
Get it in writing. Security commitments should be in your vendor contracts.
4. Data Encryption
Encrypt data at rest and in transit:
- Customer databases
- Transaction records
- Employee information
- Communications (email, messaging)
If your laptop is stolen or backup drive is lost, encryption makes the data useless to thieves.
5. Regular Software Updates
Unpatched software is the #1 technical vulnerability.
Implement a patch management process:
- POS systems
- Operating systems (Windows, macOS, Linux)
- Security software
- Network equipment firmware
- Mobile device operating systems
Set automatic updates where possible. For critical systems, test patches before deployment but deploy within 30 days.
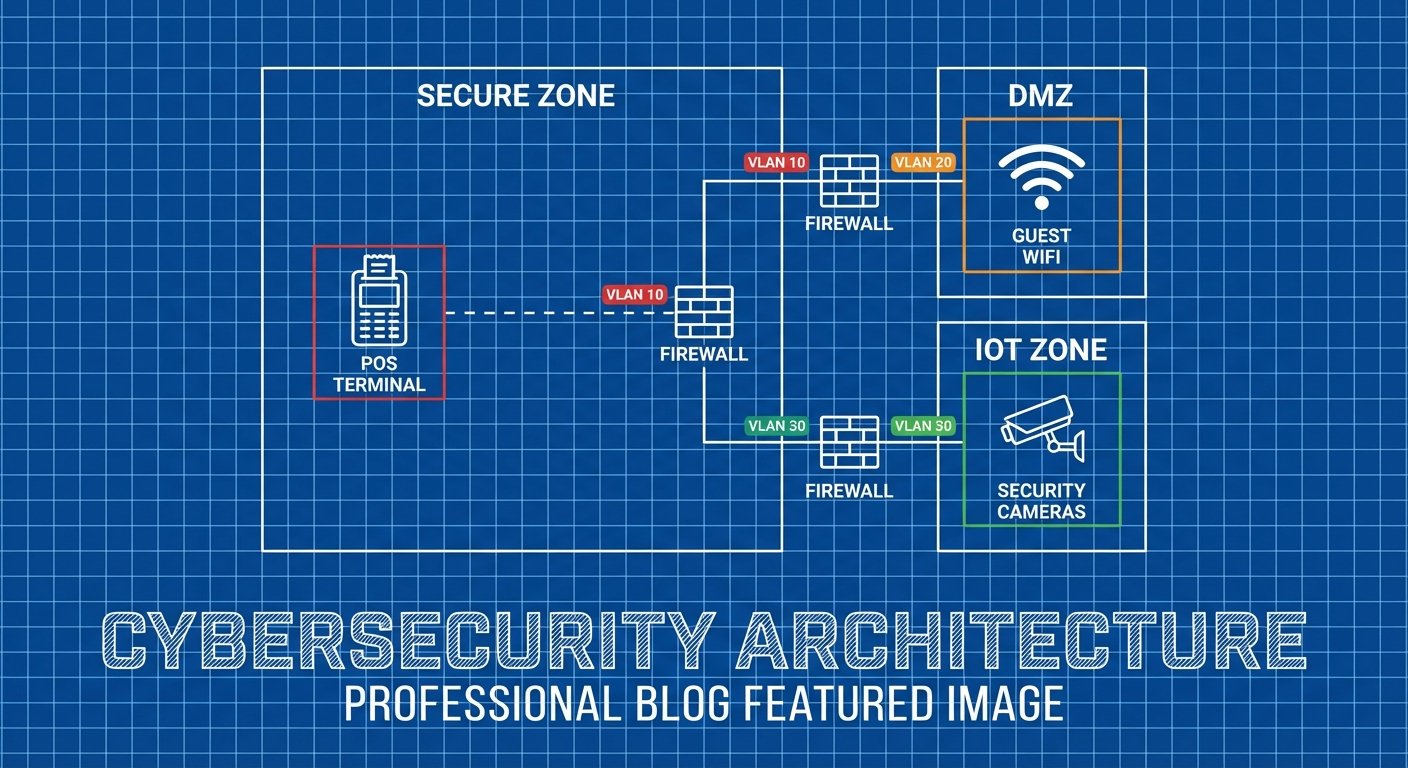
6. Network Segmentation
Don’t run your entire business on one network.
Separate networks for:
- POS/customer transactions
- Security cameras
- Guest WiFi
- Administrative systems
- Compliance/inventory tracking
If one network is compromised, the breach is contained.
7. Incident Response Planning
Hope for the best, plan for the worst.
Your incident response plan should include:
- Who to contact immediately (IT, legal, insurance, regulators)
- How to isolate affected systems
- Communication templates for customers and media
- Step-by-step recovery procedures
- Data backup restoration process
Test your plan quarterly. A plan that doesn’t work in simulation won’t work in crisis.
8. Regular Backups (The Ransomware Defense)
The best ransomware defense is never needing to pay the ransom.
Backup strategy:
- Daily automated backups of all critical systems
- Store backups offline or in isolated systems (attackers target backups)
- Test restoration monthly (backups you can’t restore are useless)
- Keep 30+ days of backup history
The 3-2-1 rule: 3 copies of data, on 2 different media types, with 1 copy offsite.
Cannabis-Specific Security Protocols
Payment Processing Security
Since you can’t use traditional credit card processors:
- Vet cashless ATM providers thoroughly
- Limit access to payment system credentials
- Monitor transactions for anomalies
- Separate payment data from customer databases
- Review payment vendor security reports quarterly
Compliance System Integration
Metrc, BioTrack, and other seed-to-sale systems are mandated by states but can be vulnerable:
- Use dedicated devices for compliance logins
- Never share compliance system credentials
- Enable all available security features
- Monitor for unauthorized access or data changes
- Maintain paper backup records for critical compliance data
ID Verification Data Handling
You’re required to scan and verify customer IDs, but this creates liability:
- Minimize data retention (delete old scans)
- Encrypt all stored ID images
- Restrict access to verification systems
- Consider third-party verification services that don’t store images
- Train staff on proper ID handling procedures
Budget-Friendly Security Investments
You don’t need enterprise budgets to significantly improve security:
Free or low-cost measures:
- Password managers: 1Password, Bitwarden ($3-5/user/month)
- MFA: Google Authenticator, Authy (free)
- Email security: Gmail/Outlook have built-in phishing protection (free)
- Security awareness: CISA Cyber Essentials Starter Kit (free)
- Backup solutions: Backblaze ($7/month per computer)
- Firewall: pfSense or OPNsense (free, open-source)
ROI on security: The average data breach costs $4.6 million. A $5,000 annual security investment is 0.1% of potential breach costs.
Industry Resources & Communities
Don’t go it alone. The cannabis security community shares threat intelligence:
Cannabis Information Sharing & Analysis Organization (Cannabis ISAO)
- Threat intelligence sharing
- Security best practices specific to cannabis
- Incident reporting and support
National Cannabis Industry Association (NCIA) - Risk Management Committee
- Industry-wide security guidance
- Regulatory compliance resources
Small Business Administration (SBA) Cybersecurity Guide
- Free security resources for small businesses
CISA Cyber Essentials
- Government-backed security fundamentals
Regulatory Considerations
Cannabis businesses face security requirements from multiple directions:
State regulations:
- Some states mandate specific security measures
- Compliance reporting may require cybersecurity documentation
- Data breach notification laws vary by state
HIPAA (for medical dispensaries):
- Protected health information requires specific safeguards
- Breach notification requirements to HHS
- Potential fines up to $50,000 per violation
Payment Card Industry (PCI) standards:
- If you process cards through cashless ATMs, PCI DSS may apply
- Failure to comply can result in loss of processing capability
Local ordinances:
- Cities and counties may have additional security requirements
- Business license renewals may require security attestations
The 2026 Cannabis Security Checklist
Use this as your baseline assessment:
Access Control
- Multi-factor authentication on all critical systems
- Strong password policies (12+ characters, unique, managed)
- Regular access reviews (remove terminated employees immediately)
- Principle of least privilege (staff only access what they need)
Network Security
- Firewall configured and regularly updated
- Network segmentation implemented
- Guest WiFi separated from business network
- VPN for remote access
Data Protection
- Customer data encrypted at rest and in transit
- Regular, tested backups (3-2-1 rule)
- Data retention policies implemented
- Secure data disposal procedures
Employee Training
- Quarterly security awareness training
- Phishing simulation exercises
- Clear security policies documented
- Incident reporting procedures established
Vendor Management
- Security assessments of all third-party vendors
- Contracts include security requirements
- Regular vendor security reviews
- Incident response coordination with vendors
Compliance
- State-mandated security measures implemented
- HIPAA compliance (for medical dispensaries)
- Data breach notification procedures
- Security documentation for audits
Incident Response
- Written incident response plan
- Designated response team
- Quarterly plan testing
- Cyber liability insurance
What’s Next?
Cybersecurity in the cannabis industry isn’t a one-time project—it’s an ongoing commitment. The threat landscape evolves constantly, regulations change, and your business grows.
Immediate action items:
- Assess current security posture: Where are your biggest gaps?
- Implement MFA everywhere: Start this week
- Train your team: Schedule first security training session
- Review vendor contracts: Identify which vendors have access to customer data
- Test your backups: Ensure you can actually restore from them
The cannabis industry is maturing, and security maturity must keep pace. The dispensaries that will thrive in 2026 and beyond are those that treat cybersecurity as a core business function—not an afterthought.
Get Deeper Cannabis Security Expertise
This article covers the fundamentals every cannabis business should implement. But comprehensive security requires specialized, ongoing guidance.
CannaSecure members get:
-
State-specific compliance security guides
-
Monthly threat intelligence reports
-
Incident response templates
-
Vendor security assessment tools
-
Private community with cannabis security professionals
-
Direct access to cybersecurity consultants
## Sign up for Canna Secure Protecting Cannabis Businesses from Breaches & Audit Failures Subscribe .nc-loop-dots-4-24-icon-o{--animation-duration:0.8s} .nc-loop-dots-4-24-icon-o *{opacity:.4;transform:scale(.75);animation:nc-loop-dots-4-anim var(--animation-duration) infinite} .nc-loop-dots-4-24-icon-o :nth-child(1){transform-origin:4px 12px;animation-delay:-.3s;animation-delay:calc(var(--animation-duration)/-2.666)} .nc-loop-dots-4-24-icon-o :nth-child(2){transform-origin:12px 12px;animation-delay:-.15s;animation-delay:calc(var(--animation-duration)/-5.333)} .nc-loop-dots-4-24-icon-o :nth-child(3){transform-origin:20px 12px} @keyframes nc-loop-dots-4-anim{0%,100%{opacity:.4;transform:scale(.75)}50%{opacity:1;transform:scale(1)}} Email sent! Check your inbox to complete your signup. No spam. Unsubscribe anytime.
About CannaSecure
CannaSecure provides specialized cybersecurity education, tools, and consulting for the cannabis industry. We understand the unique challenges of operating in this highly regulated, high-risk sector and provide practical, affordable security solutions for dispensaries, cultivators, and cannabis businesses of all sizes.
Legal Disclaimer: This article provides general cybersecurity guidance and does not constitute legal, compliance, or professional security advice. Cannabis businesses should consult with qualified cybersecurity professionals and legal counsel for specific guidance tailored to their operations and jurisdiction.
Share this article: Help other cannabis businesses improve their security—share this guide with your network.