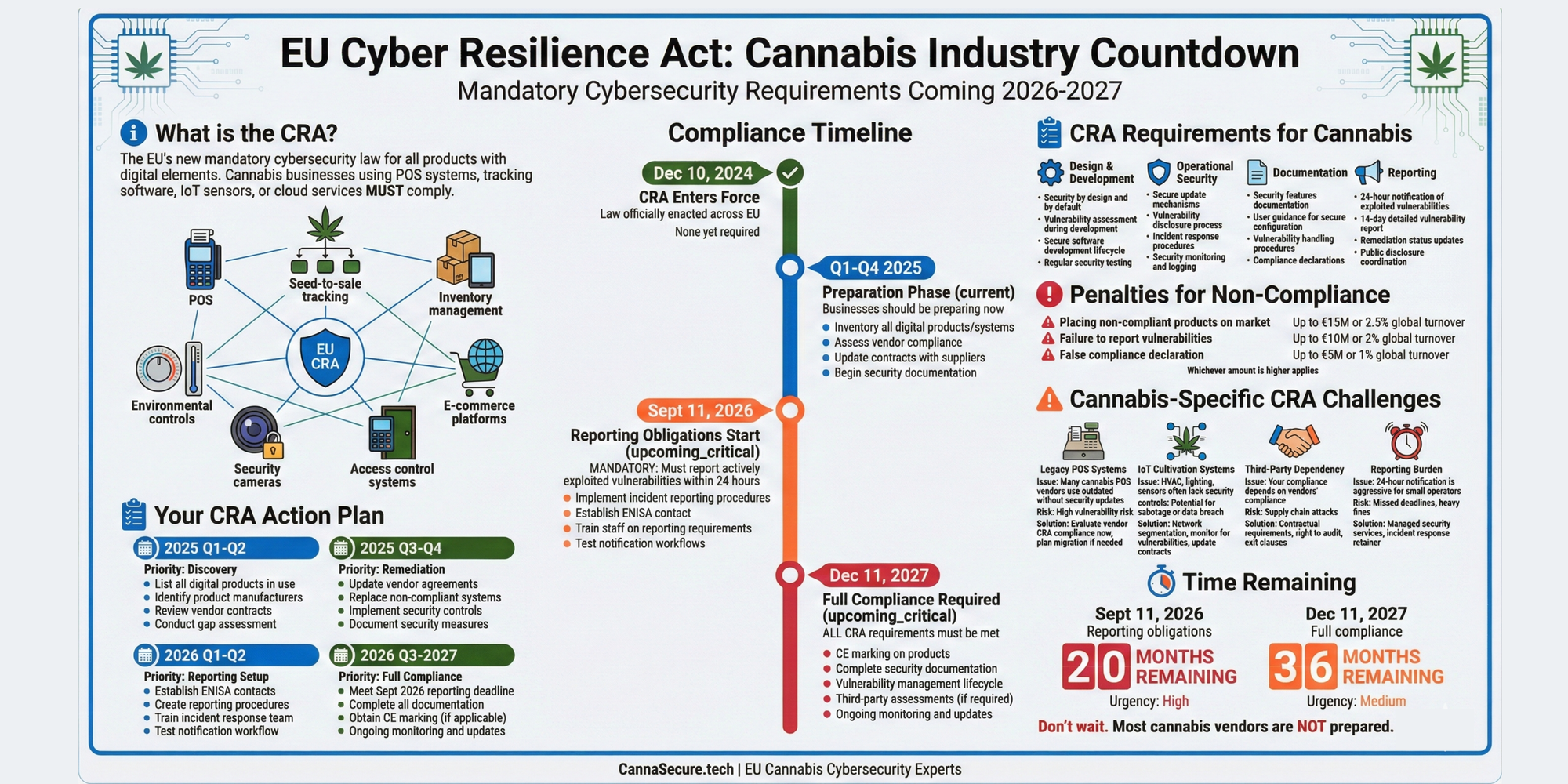
The EU’s most significant cybersecurity regulation in a decade is coming—and most cannabis businesses don’t know they’re in scope.
Quick Reference:
- Key Deadlines: September 11, 2026 (reporting obligations) | December 11, 2027 (full compliance)
- Applies To: All “products with digital elements” sold in the EU market
- Maximum Penalties: €15 million or 2.5% of global annual turnover
- Cannabis Impact: POS systems, seed-to-sale tracking, IoT sensors, HVAC controls, security systems
Introduction: The EU’s New Mandatory Cybersecurity Law
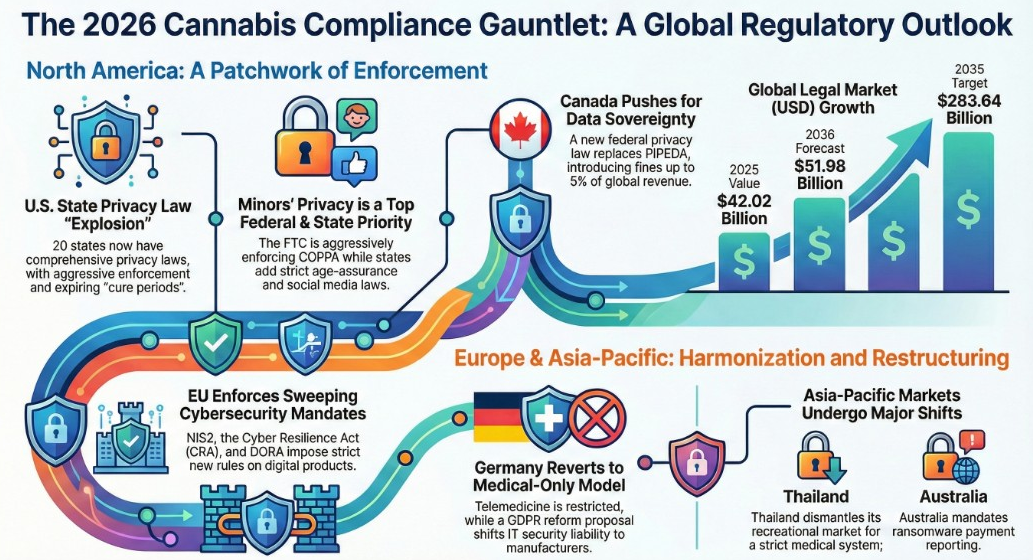
On December 10, 2024, the European Union’s Cyber Resilience Act (CRA) officially entered into force, marking the most sweeping mandatory cybersecurity regulation for digital products in EU history. Unlike sector-specific regulations, the CRA applies horizontally across all industries—including cannabis.
For cannabis businesses operating in or selling to European markets, this regulation represents both a significant compliance challenge and a potential competitive advantage. Companies that prepare now will be positioned as trusted partners for enterprise clients and government contracts. Those who ignore it risk substantial fines and market exclusion.
What is the Cyber Resilience Act?
The CRA (Regulation EU 2024/2847) establishes mandatory cybersecurity requirements for all “products with digital elements” sold on the EU market. This includes hardware, software, and their remote data processing solutions—covering everything from consumer IoT devices to industrial control systems.
The regulation requires:
- Security by design: Products must be developed with cybersecurity as a core requirement, not an afterthought
- Lifecycle security: Manufacturers must maintain security throughout the product’s expected lifespan
- Vulnerability management: Active monitoring, disclosure, and patching of security vulnerabilities
- Incident reporting: Mandatory 24-hour reporting of actively exploited vulnerabilities to EU authorities
- CE marking: Products must display CE certification indicating CRA compliance
Why the CRA Affects Cannabis Businesses
Cannabis operations are increasingly technology-dependent. From seed-to-sale tracking mandated by regulators to environmental controls that optimize cultivation, digital systems permeate every aspect of the modern cannabis business. If you’re operating in or selling products to EU markets, nearly every digital tool you use—or manufacture—falls under CRA scope.
The CRA doesn’t care whether you’re a cannabis-specific technology vendor or a general-purpose POS manufacturer who happens to have cannabis clients. If the product contains digital elements and reaches the EU market, compliance is mandatory.
Critical Deadlines
September 11, 2026 – Reporting Obligations Begin
From this date, manufacturers must report actively exploited vulnerabilities within 24 hours to the Computer Security Incident Response Team (CSIRT) of their member state and to the European Union Agency for Cybersecurity (ENISA). This applies to all products currently on the market—not just new releases.
December 11, 2027 – Full Compliance Required
All CRA requirements become enforceable. Products without CE marking indicating CRA compliance cannot be sold in the EU. This includes cybersecurity by design requirements, documentation, Software Bills of Materials (SBOMs), and ongoing vulnerability management.
Penalties for Non-Compliance
The CRA establishes a tiered penalty structure:
- Essential cybersecurity requirement violations: Up to €15 million or 2.5% of total worldwide annual turnover, whichever is higher
- Other CRA obligation violations: Up to €10 million or 2% of global annual turnover
- Providing incorrect information to authorities: Up to €5 million or 1% of global annual turnover
Beyond fines, non-compliant products can be banned from the EU market entirely, and market surveillance authorities can mandate product recalls.
Section 1: Does the CRA Apply to Your Cannabis Business?
The CRA’s scope is intentionally broad, covering approximately 90% of digital products sold in the EU. Understanding whether—and how—the regulation applies to your business is the essential first step.
What are “Products with Digital Elements”?
The CRA defines a product with digital elements (PDE) as “any software or hardware product and its remote data processing solutions, including software or hardware components being placed on the market separately.”
More specifically, PDEs include products “whose intended or reasonably foreseeable use includes a direct or indirect logical or physical data connection to a device or network.”
In practical terms: if it connects to a network, receives updates, or processes data remotely, it’s likely in scope.
Cannabis Industry Systems Covered by the CRA
Point-of-Sale (POS) Systems
Cannabis-specific POS platforms like Flowhub, Dutchie, or custom solutions are clearly within scope. These systems handle financial transactions, integrate with seed-to-sale tracking, and often connect to cloud backends—all characteristics that bring them under CRA jurisdiction.
Seed-to-Sale Tracking Software
Compliance tracking platforms mandated by regulators (METRC integrations, BioTrack, etc.) fall squarely within CRA scope. These systems maintain logical data connections and often process information remotely.
Inventory Management Systems
Any inventory management software that connects to networks or cloud services requires CRA compliance, whether cannabis-specific or general-purpose solutions adapted for the industry.
Environmental Control Systems
Climate control systems for cultivation facilities—HVAC, lighting automation, CO2 regulation, irrigation controllers—increasingly feature network connectivity and remote monitoring capabilities. IoT sensors measuring temperature, humidity, and soil conditions are explicitly targeted by the CRA.
Security Cameras and Access Control
IP-connected security cameras, badge access systems, and alarm monitoring platforms are all PDEs under the CRA. Given cannabis security requirements, these systems are ubiquitous in the industry.
E-Commerce Platforms
Online ordering systems, delivery management software, and customer-facing applications all fall within scope if they connect to networks or process data remotely.
Manufacturer vs. Distributor Obligations
The CRA establishes different obligations based on your role in the supply chain:
Manufacturers bear the primary compliance burden. They must ensure products meet essential cybersecurity requirements, conduct risk assessments, create technical documentation, provide SBOMs, and handle vulnerability reporting. If you develop cannabis technology in-house, you’re a manufacturer.
Importers who bring products into the EU market must verify that manufacturers have fulfilled their obligations and that proper CE marking and documentation exist.
Distributors must verify that products bear the required CE marking and that manufacturers and importers have met their obligations. If you discover non-compliance, you cannot make the product available until issues are resolved.
Self-Assessment Checklist
Answer these questions to determine your CRA exposure:
- Do you manufacture, import, or distribute digital products in EU markets?
- Do any of your products connect to networks, receive updates, or process data remotely?
- Do you use third-party technology vendors for critical business systems?
- Do your technology vendors sell products in EU markets?
- Have your vendors communicated CRA compliance plans?
If you answered “yes” to questions 1-2, you have direct CRA obligations. If you answered “yes” to questions 3-5, you have supply chain risk that requires vendor assessment.
Section 2: CRA Security Requirements
The CRA establishes comprehensive cybersecurity requirements that apply throughout a product’s lifecycle. Understanding these requirements is essential for both compliance planning and vendor evaluation.
Cybersecurity by Design and by Default
Products must be designed, developed, and produced to ensure an appropriate level of cybersecurity based on their risk profile. The CRA requires that products are delivered:
- Without known exploitable vulnerabilities
- With secure-by-default configurations
- With appropriate access controls and authentication mechanisms
- With encryption for data at rest and in transit using state-of-the-art mechanisms
- With integrity protection for stored and transmitted data
- With data minimization—collecting only necessary information
- With resilience against denial-of-service attacks
- With minimal attack surface exposure
Vulnerability Management During Product Lifecycle
Manufacturers must implement comprehensive vulnerability handling throughout the product’s expected lifespan:
- Identification and documentation: Maintain awareness of vulnerabilities and affected components
- Software Bill of Materials (SBOM): Document all components including third-party and open-source elements in a machine-readable format
- Coordinated disclosure: Establish policies for handling vulnerability reports from external researchers
- Remediation: Provide free security updates that can be distributed securely
- Communication: Inform users about vulnerabilities and required security measures
Secure Software Updates
The CRA mandates that manufacturers:
- Provide mechanisms to securely distribute updates
- Ensure updates are timely and free of charge
- Include advisory messages explaining user actions required
- Enable automatic update capabilities where appropriate
- Support products with security updates for their entire expected lifespan
Security Documentation Requirements
Technical documentation must include:
- General product description and intended purpose
- Design and development information demonstrating cybersecurity integration
- Cybersecurity risk assessment addressing Article 10(2) requirements
- List of harmonized standards applied (full or partial)
- Evidence of conformity with essential requirements
- Vulnerability handling procedures
- SBOM documentation
User documentation must provide:
- Clear installation and operation instructions
- Security configuration guidance
- Information about the manufacturer’s vulnerability handling contact
- Product support period and security update availability
CE Marking Compliance
CE marking indicates compliance with all applicable EU regulations, now including CRA cybersecurity requirements. Products without appropriate CE marking cannot legally be sold in the EU market after December 11, 2027.
The manufacturer prepares an EU declaration of conformity affirming that the product meets all essential requirements and affixes the CE marking. This marking can only be applied after appropriate conformity assessment procedures have been completed.
Third-Party Assessment for Critical Products
The CRA categorizes products into risk tiers:
Default Category (~90% of products): Manufacturers can self-assess compliance through internal procedures and technical documentation.
Important Class I: Requires conformity assessment by an accredited notified body or application of harmonized standards. Includes categories like identity management systems and password managers.
Important Class II: Requires mandatory third-party assessment by notified bodies. Includes operating systems, network management systems, and industrial automation controllers.
Critical Category: Subject to the most stringent requirements and European cybersecurity certification. Includes products essential for critical infrastructure protection.
Most cannabis industry technology falls into the default or Important Class I categories, allowing self-assessment or harmonized standard application.
Section 3: Reporting Obligations (Starting September 2026)
The September 11, 2026 deadline represents the first mandatory compliance milestone—and it applies to products already on the market, not just new releases. Understanding these reporting obligations is crucial for immediate planning.
What Constitutes an “Actively Exploited Vulnerability”?
An actively exploited vulnerability is a security flaw in a product with digital elements that attackers are currently using in real-world attacks. The key distinction is between:
- Theoretical vulnerabilities: Known security weaknesses without evidence of exploitation (reporting not triggered)
- Actively exploited vulnerabilities: Confirmed instances of attackers leveraging the vulnerability (mandatory reporting required)
The distinction matters because the 24-hour clock starts only when the manufacturer becomes aware that a vulnerability is being actively exploited. However, manufacturers are expected to maintain reasonable monitoring to detect such exploitation.
The 24-Hour Initial Notification Timeline
When a manufacturer becomes aware of an actively exploited vulnerability, they must submit an early warning notification within 24 hours. This initial notification must include:
- Information about the vulnerability (to the extent known)
- Member states where the affected product is known to be available
- Whether the exploitation appears malicious in nature
- Preliminary impact assessment
The 24-hour window is strict. Manufacturers without established monitoring and response processes will struggle to meet this requirement—making preparation before September 2026 essential.
Subsequent Notification Requirements
72-hour notification: A more detailed vulnerability notification providing:
- Additional technical details about the vulnerability
- Preliminary assessment of severity and impact
- Any available mitigating measures
- Information about exploiting actors (if known)
14-day final report (for vulnerabilities): Submitted once corrective measures are available:
- Complete vulnerability analysis
- Severity and impact documentation
- Information about malicious actors involved
- Details of security updates or corrective measures provided
- Root cause analysis and prevention measures implemented
30-day final report (for severe incidents): For incidents impacting product security beyond specific vulnerabilities:
- Complete incident documentation
- Impact assessment across affected users
- Remediation steps taken
- Lessons learned and preventive measures
Who to Report To: ENISA and National Authorities
Notifications are submitted through the CRA Single Reporting Platform (SRP), which ENISA is developing for launch by September 11, 2026. The notification is addressed to:
Primary recipient: The Computer Security Incident Response Team (CSIRT) designated as coordinator in the member state where the manufacturer has its main EU establishment
Simultaneous recipient: ENISA (European Union Agency for Cybersecurity)
The CSIRT receiving the notification will disseminate information to CSIRTs in other member states where the affected product is available. This ensures coordinated response across the EU.
For non-EU manufacturers, the CSIRT is determined based on where cybersecurity-related decisions for their products are primarily made.
Documentation Requirements
Manufacturers must maintain documentation supporting their reporting obligations:
- Evidence of awareness date (when exploitation was discovered)
- Notification submissions and timestamps
- Communication with affected users
- Corrective measure development and deployment records
- Any intermediate reports requested by authorities
This documentation becomes critical during regulatory audits and enforcement actions.
Incident Response Procedures
To meet the September 2026 deadline, cannabis technology providers need established incident response procedures including:
- Monitoring capabilities: Systems to detect when vulnerabilities in your products are being exploited
- Assessment processes: Procedures to evaluate severity and determine reporting obligations
- Communication channels: Established contacts with relevant CSIRTs
- Notification templates: Pre-drafted reporting formats to meet 24-hour timelines
- User communication plans: Processes to inform affected customers
- Remediation workflows: Procedures for developing and deploying security updates
Section 4: Cannabis-Specific CRA Challenges
While the CRA applies uniformly across industries, cannabis businesses face unique challenges that require specific attention during compliance planning.
Legacy Systems Without Security Updates
Cannabis technology evolved rapidly during market expansion, and many operations run systems that weren’t designed with long-term security support in mind. The CRA requires vulnerability management throughout a product’s expected lifespan, creating challenges for:
- Older cultivation management systems without manufacturer support
- Custom integrations built by vendors who’ve exited the market
- Hardware devices with embedded firmware that can’t be updated
Mitigation strategies:
- Inventory all digital systems and verify manufacturer support status
- Plan replacement timelines for unsupported systems before December 2027
- Implement network segmentation to isolate legacy devices that can’t be updated
- Document compensating controls for systems that can’t meet full CRA requirements
Third-Party Vendor Compliance
Most cannabis businesses rely heavily on third-party technology providers. A critical question: does your POS vendor know about the CRA?
Many cannabis technology vendors—particularly U.S.-based companies—may not be aware of their CRA obligations or may not prioritize EU compliance. This creates risk for cannabis operators who depend on these systems.
Actions to take:
- Contact vendors directly about CRA compliance plans
- Request written confirmation of September 2026 reporting readiness
- Evaluate backup vendors who are committed to CRA compliance
- Include CRA compliance requirements in vendor contracts and renewals
IoT Devices in Cultivation
Environmental monitoring and control systems in cultivation facilities often feature dozens or hundreds of connected sensors. These IoT devices are explicitly targeted by the CRA, and many current products don’t meet essential requirements.
Common compliance gaps in cultivation IoT include:
- Devices shipped with default credentials
- No automatic update mechanisms
- Inadequate encryption for sensor data
- Unknown or undocumented components in device firmware
Risk areas to assess:
- Environmental sensors (temperature, humidity, CO2, light)
- Irrigation and fertigation controllers
- HVAC automation systems
- Lighting control systems
- Security sensors and access control devices
Cloud vs. On-Premise Security Considerations
The CRA’s scope extends to “remote data processing solutions” that products depend on to function. This means cloud backends, APIs, and companion services are in scope when they’re integral to product operation.
However, pure SaaS and PaaS offerings that aren’t tied to specific PDEs fall outside CRA scope (though they may face obligations under NIS2 or GDPR).
Assessment framework:
- If your on-premise software requires cloud connectivity to function, both the software and cloud service are in scope
- If cloud services are optional enhancements, scope may be limited
- Mobile applications that accompany hardware products are in scope
- Administrative dashboards for IoT devices are in scope
Supply Chain Risk Management
The CRA makes supply chain security a legal obligation, not just a best practice. Manufacturers must verify the integrity of third-party components, including open-source software, to ensure they don’t compromise product security.
For cannabis technology providers, this means:
- Maintaining SBOMs that document all dependencies
- Monitoring vulnerability databases for third-party component issues
- Establishing procedures to respond when upstream vulnerabilities are discovered
- Contractual requirements for security practices from component suppliers
Section 5: CRA Compliance Roadmap
With September 2026 less than nine months away and full compliance required by December 2027, cannabis businesses need actionable timelines. This roadmap provides a phased approach to CRA readiness.
2025 Q1-Q2: Inventory Digital Products
Immediate actions:
- Create a comprehensive inventory of all digital products your organization manufactures or sells
- Identify all third-party digital products critical to operations
- Determine your role (manufacturer, importer, distributor) for each product
- Classify products by CRA risk category (default, important, critical)
Documentation to create:
- Product inventory spreadsheet with technical specifications
- Vendor contact list with compliance responsibility assignments
- Gap analysis identifying products lacking essential CRA requirements
2025 Q3-Q4: Vendor Assessments and Contract Updates
Vendor evaluation:
- Send formal inquiries to all technology vendors regarding CRA compliance
- Request evidence of SBOM capabilities and vulnerability management processes
- Evaluate vendor readiness for September 2026 reporting obligations
- Identify vendors requiring replacement due to compliance gaps
Contract modifications:
- Add CRA compliance clauses to new agreements and renewals
- Require notification of actively exploited vulnerabilities
- Establish SLA expectations for security updates
- Include audit rights for compliance verification
2026 Q1-Q2: Implement Reporting Procedures
Internal process development:
- Establish vulnerability monitoring capabilities for your products
- Create incident response procedures meeting 24-hour notification requirements
- Designate personnel responsible for CRA reporting
- Register with relevant CSIRTs and familiarize with the Single Reporting Platform
Testing and validation:
- Conduct tabletop exercises simulating vulnerability discovery and reporting
- Verify notification procedures can meet 24-hour timelines
- Test user communication workflows
- Document procedures for regulatory review
2026 Q3: September Reporting Deadline
September 11, 2026 – Reporting obligations take effect:
- All actively exploited vulnerabilities must be reported within 24 hours
- This applies to existing products already on the market
- Monitoring and response systems must be fully operational
- Documentation must demonstrate compliance capability
2027: Full Compliance by December
December 11, 2027 – All requirements enforceable:
- Products must meet all essential cybersecurity requirements
- CE marking required for EU market access
- Technical documentation complete and available
- SBOM maintenance and ongoing vulnerability management active
- Secure update mechanisms functional
Monthly Compliance Checklist [Premium Resource]
Comprehensive monthly milestone tracking is available in the CRA Toolkit for Cannabis, including specific tasks, responsible parties, and documentation templates.
Section 6: Vendor Management Under CRA
For most cannabis businesses, achieving CRA compliance depends heavily on third-party technology providers. Effective vendor management is essential.
Questions to Ask Your POS/Software Vendors
When evaluating vendor CRA readiness, ask:
- Are you aware of the EU Cyber Resilience Act and its applicability to your products?
- What is your timeline for full CRA compliance?
- Will your products be CRA-compliant by September 11, 2026 (reporting obligations)?
- Will your products carry appropriate CE marking by December 11, 2027?
- Do you maintain Software Bills of Materials (SBOMs) for your products?
- What is your vulnerability disclosure and management process?
- How quickly can you provide security updates when vulnerabilities are discovered?
- What is your support period for the products we’re using?
- How will you notify us of actively exploited vulnerabilities?
- Can you provide documentation of your secure development practices?
Contract Clauses to Require CRA Compliance
Incorporate these provisions in vendor agreements:
Compliance commitment: “Vendor represents and warrants that all products provided under this agreement will comply with EU Regulation 2024/2847 (Cyber Resilience Act) by the applicable compliance deadlines.”
Notification requirements: “Vendor shall notify Customer within [24/48] hours of becoming aware of any actively exploited vulnerability affecting products provided under this agreement.”
SBOM provision: “Upon request, Vendor shall provide Customer with current Software Bills of Materials in [CycloneDX/SPDX] format for all products covered by this agreement.”
Update obligations: “Vendor shall provide security updates addressing discovered vulnerabilities without additional charge for the duration of the product support period.”
Documentation access: “Vendor shall maintain and, upon reasonable request, provide access to technical documentation demonstrating CRA compliance.”
Indemnification: “Vendor shall indemnify Customer against penalties, fines, or damages arising from Vendor’s failure to comply with CRA requirements.”
Alternative Vendor Evaluation
If current vendors are unable or unwilling to commit to CRA compliance, evaluate alternatives using these criteria:
- Documented CRA compliance roadmap
- Demonstrated vulnerability management capabilities
- Established security development practices
- Transparent SBOM documentation
- Clear product support lifecycle commitments
- EU market presence and regulatory familiarity
In-House vs. Managed Security Services
For cannabis operations without dedicated security resources, consider:
Managed Security Service Providers (MSSPs): Can provide vulnerability monitoring, incident response, and compliance documentation support—valuable for meeting September 2026 reporting requirements.
Virtual CISO services: Provide strategic security leadership and regulatory compliance guidance without full-time executive costs.
Security consulting: Useful for gap assessments, compliance roadmap development, and vendor evaluation.
Vendor Audit Templates [Premium Resource]
Comprehensive vendor assessment questionnaires and audit checklists are available in the CRA Toolkit for Cannabis.
Section 7: Integration with Existing Compliance
The CRA doesn’t exist in isolation. Cannabis businesses operating in EU markets likely face multiple overlapping regulatory requirements. Understanding these overlaps enables efficient compliance management.
CRA + GDPR Overlap
Both regulations address security and incident reporting, but with different focuses:
GDPR protects personal data and requires breach notification within 72 hours to data protection authorities. It applies to organizations processing EU residents’ personal data.
CRA protects product security and requires vulnerability reporting within 24 hours to CSIRTs. It applies to products with digital elements sold in the EU market.
Integration opportunities:
- Risk assessment methodologies can address both product security and data protection
- Incident response procedures can be unified to handle both vulnerability reports and breach notifications
- Documentation practices can serve both regulatory requirements
- Many GDPR security controls directly support CRA essential requirements
Organizations already GDPR-compliant have a foundation for CRA compliance, particularly around security controls, incident response, and documentation practices.
CRA + EU-GMP Cybersecurity
Cannabis businesses operating under EU Good Manufacturing Practice (EU-GMP) standards already face quality and traceability requirements that overlap with CRA concerns:
Existing EU-GMP requirements:
- Computerized systems validation
- Data integrity controls
- Audit trail maintenance
- Access control and authorization
CRA additions:
- Vulnerability management throughout product lifecycle
- Mandatory incident reporting
- Security-by-design development practices
- CE marking for digital products
EU-GMP certified operations may find that existing quality management systems provide infrastructure adaptable for CRA compliance, particularly around documentation and change management.
CRA + ISO 27001
ISO 27001 provides a voluntary framework for information security management systems (ISMS). Organizations with ISO 27001 certification have established practices that support CRA compliance:
ISO 27001 foundations applicable to CRA:
- Risk assessment and treatment methodologies
- Security policy development and governance
- Incident management procedures
- Supplier relationship security
- Asset management and inventory
- Vulnerability management processes
Key distinction: ISO 27001 focuses on organizational security, while CRA focuses on product security. However, the frameworks share common foundations in risk management, secure development, and incident response.
Organizations pursuing both frameworks can map ISO 27001 Annex A controls to CRA essential requirements, reducing duplicate effort and creating unified compliance programs.
Unified Compliance Framework
Rather than treating each regulation as a separate initiative, cannabis businesses should develop integrated compliance programs:
Shared foundations:
- Unified risk assessment methodology addressing product, organizational, and data protection risks
- Consolidated incident response procedures with branching workflows for different notification requirements
- Integrated documentation systems that support multiple regulatory evidencing needs
- Coordinated audit calendars and internal assessment programs
Practical implementation:
- Map CRA essential requirements to existing compliance frameworks
- Identify gaps requiring new controls or processes
- Develop unified policies addressing multiple regulatory requirements
- Implement integrated monitoring and reporting systems
- Coordinate audit preparation across frameworks
Section 8: CRA Toolkit for Cannabis [Premium Resource]
The complete CRA Toolkit for Cannabis includes comprehensive resources for compliance preparation and ongoing management.
Product Inventory Template
Structured spreadsheet for documenting all digital products, including:
- Product identification and classification
- Manufacturer and vendor information
- CRA risk category determination
- Support lifecycle and update status
- Component documentation status
- Compliance gap identification
Vulnerability Management Procedures
Step-by-step procedures for:
- Vulnerability monitoring and detection
- Severity assessment and prioritization
- Remediation planning and execution
- Update development and deployment
- User notification workflows
- Documentation and evidence retention
Incident Reporting Templates
Pre-formatted notification templates aligned with CRA requirements:
- 24-hour early warning notification
- 72-hour vulnerability notification
- Final report documentation
- User communication templates
- Evidence collection checklists
Vendor Assessment Questionnaire
Comprehensive questionnaire covering:
- CRA awareness and compliance commitment
- Security development practices
- Vulnerability management capabilities
- SBOM documentation
- Update and support policies
- Incident notification procedures
Gap Analysis Checklist
Detailed assessment tool evaluating compliance status against:
- Essential cybersecurity requirements (Annex I, Part I)
- Vulnerability handling requirements (Annex I, Part II)
- Documentation requirements
- Conformity assessment readiness
- Reporting procedure preparedness
Access the complete CRA Toolkit for Cannabis through CISO Marketplace premium membership.
Conclusion: CRA as Market Differentiator
The EU Cyber Resilience Act represents the most significant mandatory cybersecurity regulation for digital products in EU history. For cannabis businesses, it creates both challenges and opportunities.
The Challenge
Compliance requires substantial preparation across technology, processes, and supply chain relationships. The September 2026 reporting deadline leaves limited time for organizations that haven’t begun preparation.
The Opportunity
Early CRA compliance positions cannabis businesses as trusted partners in an industry increasingly focused on security and regulatory adherence. As enterprise clients, government contracts, and institutional investors demand verified security practices, CRA compliance becomes a competitive differentiator.
Compliant businesses will:
- Access EU markets without disruption
- Win contracts with security-conscious enterprise operators
- Demonstrate regulatory maturity to investors and partners
- Reduce breach risk and associated costs
- Build reputation as industry security leaders
Non-compliant businesses will:
- Face potential market exclusion from EU
- Lose competitive positioning for security-sensitive contracts
- Risk substantial financial penalties
- Assume increased breach liability
- Signal regulatory immaturity to sophisticated partners
Next Steps
- Assess your exposure: Determine which products and systems fall under CRA scope
- Engage vendors: Contact technology providers about compliance plans
- Begin documentation: Start building product inventories and gap analyses
- Establish procedures: Develop incident response and reporting capabilities
- Seek expertise: Consider consulting support for complex compliance requirements
The cannabis industry’s rapid technology adoption created extraordinary operational capabilities. The CRA ensures those capabilities include appropriate security foundations. Organizations that embrace this requirement will lead the industry’s next evolution toward mature, trusted, and resilient operations.
This guide was prepared for educational purposes and does not constitute legal advice. Organizations should consult qualified legal counsel for compliance guidance specific to their circumstances.
About CISO Marketplace
CISO Marketplace provides cybersecurity consulting, compliance assessment, and security program development for businesses navigating complex regulatory requirements. With 15+ years of experience and 400+ completed security assessments, we help organizations build security programs that meet regulatory obligations while enabling business growth.
Contact us for CRA compliance assessment and preparation services.