The STIIIZY breach came through a POS vendor. MJ Freeway disrupted dispensaries across multiple states. Your security is only as strong as your weakest vendor.
The Vendor Problem
Here’s an uncomfortable truth: you can have perfect internal security and still get breached through a vendor.
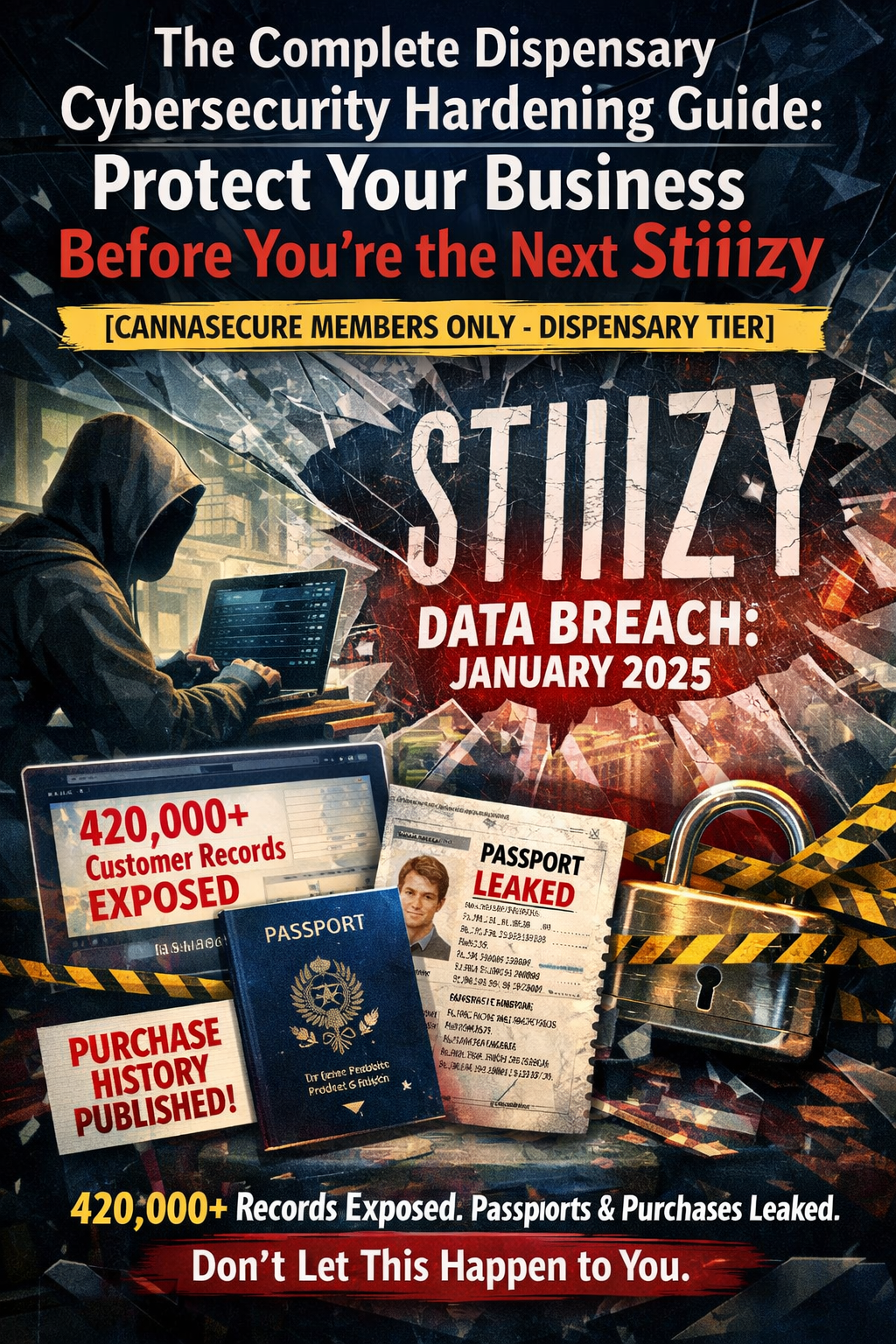
In late 2024, STIIIZY—one of California’s largest cannabis brands—discovered that 420,000+ customer records had been stolen. The attackers didn’t hack STIIIZY directly. They compromised a third-party point-of-sale vendor that had access to customer data.
Names. Addresses. Government IDs. Medical cannabis cards. Purchase histories. All exposed because someone else’s security failed.
This isn’t a new phenomenon. In 2017 and 2018, MJ Freeway—a major cannabis compliance software provider—suffered repeated breaches that disrupted dispensary operations across multiple states. Some operators couldn’t process sales for days.
The pattern is clear: Cannabis businesses depend heavily on external vendors, and those vendors are now primary attack targets.
Why Attackers Target Your Vendors
Think about it from an attacker’s perspective:
Direct Attack:
- Target one dispensary
- Maybe get a few thousand customer records
- Have to repeat the process for every target
Vendor Attack:
- Target one software provider
- Get access to hundreds of dispensaries at once
- One breach, massive payoff
The economics favor attacking vendors. Everest (the ransomware group behind the STIIIZY breach) has built an entire business model around this—they function as “initial access brokers,” selling access to vendor systems to other criminal groups.
Your Vendor Attack Surface
Before you can secure your vendor relationships, you need to understand what you’re actually exposed to.
Map Your Vendors
Create a complete inventory of every third party that has access to:
Customer Data:
- Point-of-sale systems
- E-commerce platforms
- Loyalty program providers
- Delivery platforms
- Age verification services
- ID scanning solutions
- Customer relationship management (CRM)
- Email marketing platforms
Business Operations:
- Seed-to-sale/track-and-trace (METRC integrations)
- Inventory management
- Accounting software
- Payroll providers
- HR systems
Technology Infrastructure:
- Cloud hosting providers
- Managed IT services
- Security monitoring
- Backup providers
- Payment processors
Physical Access:
- Security guard services
- Alarm monitoring companies
- HVAC/maintenance contractors
- Cleaning services
Categorize by Risk
Not all vendors are equal. Categorize each by:
Tier 1 - Critical (Highest Risk):
- Direct access to customer PII
- Access to financial systems
- Integration with METRC/compliance systems
- Can impact your ability to operate
Tier 2 - Important (Medium Risk):
- Access to internal business data
- Physical access to facilities
- Supporting services with some data exposure
Tier 3 - Standard (Lower Risk):
- Limited data access
- Easily replaceable services
- Minimal operational impact if compromised
Your Tier 1 vendors need the most scrutiny. A breach of your POS system is catastrophic. A breach of your office supply vendor? Inconvenient, but manageable.
The Vendor Security Assessment
For every Tier 1 vendor—and ideally Tier 2 as well—you should conduct a security assessment before signing a contract and periodically thereafter.
The Essential Questions
Here’s what you need to ask:
1. Security Certifications
“Do you have SOC 2 Type II certification?”
SOC 2 (Service Organization Control 2) is the gold standard for vendor security. Type II means they’ve been audited over a period of time, not just at a single point.
- SOC 2 Type II: Best - continuous compliance verified
- SOC 2 Type I: Good - controls exist but not tested over time
- ISO 27001: Also good - international security standard
- Nothing: Red flag
If they can’t provide a SOC 2 report or equivalent, dig deeper into why not. Small vendors may not have the resources for formal certification, but they should be able to explain their security program in detail.
“Can I review your most recent SOC 2 report?”
They should provide it under NDA. Read Section 5 (if present) for any exceptions or issues noted by auditors.
2. Data Handling
“What specific data do you need access to, and why?”
Vendors often request more access than necessary. Challenge any request for data that isn’t essential to the service they provide.
“Where is our data stored geographically?”
Important for compliance. If you’re a California dispensary, you may have CCPA obligations that require knowing where data resides.
“Is our data encrypted at rest and in transit?”
Both should be yes. Ask specifically about:
- Encryption algorithm (AES-256 is standard)
- Key management (who controls encryption keys?)
- TLS version for data in transit (should be 1.2 or higher)
“Is our data segregated from other customers’ data?”
Multi-tenant systems are common, but your data should be logically separated. Ask how they prevent one customer from accessing another’s data.
“What happens to our data when we terminate the contract?”
You want a clear data deletion policy with certification. “We’ll delete it” isn’t enough—you want documented procedures and proof of deletion.
3. Access Controls
“Who in your organization can access our data?”
The answer should be “only those with a business need.” Ask for specifics:
- How many people?
- What roles?
- How is access approved?
“How do you handle employee terminations?”
Access should be revoked immediately. Ask about their offboarding procedures.
“Do you require multi-factor authentication for access to customer data?”
This should be a firm yes. If they’re not using MFA internally, walk away.
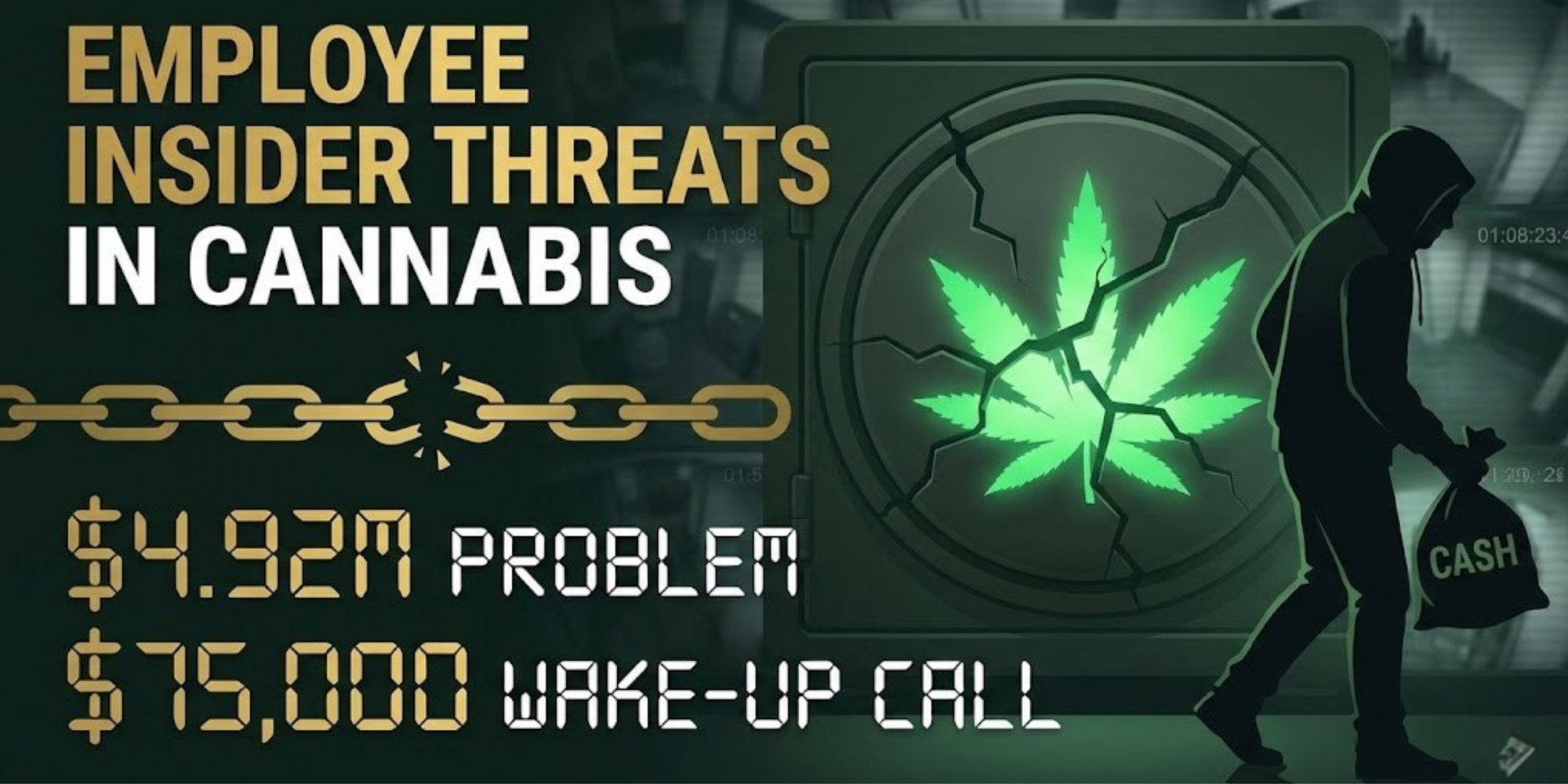
“Do you conduct background checks on employees with data access?”
Especially important for cannabis—your vendors’ employees should be vetted similarly to your own.
4. Incident Response
“What is your incident notification timeline?”
The industry standard expectation is 72 hours or less. California’s data breach law requires notification “without unreasonable delay.” Your vendor should commit to telling you within 24-48 hours.
“Can you provide a copy of your incident response plan?”
They should have one. If they don’t, that tells you a lot.
“When was your last security incident, and what happened?”
This is a trick question. Any vendor that’s been operating for more than a few years has probably had something happen. “Never” is either a lie or a sign they don’t have detection capabilities. Look for honest answers about incidents and how they were handled.
“Do you have cyber insurance?”
They should. Ask for:
- Coverage limits
- What’s covered (data breach, business interruption?)
- Whether your data is covered under their policy
5. Security Testing
“When was your last penetration test, and can we see the executive summary?”
Annual penetration testing is the minimum. They should be willing to share results (or at least a summary) under NDA.
“Do you have a vulnerability disclosure or bug bounty program?”
Not required, but a good sign of security maturity.
“How quickly do you patch critical vulnerabilities?”
Industry standard: critical vulnerabilities should be patched within 24-48 hours. High severity within 7 days.
6. Compliance
“Are you compliant with CCPA/CPRA?”
If they handle California consumer data, they should be.
“Are you HIPAA compliant?”
Required if they’ll handle medical cannabis patient information.
“Have you worked with cannabis businesses before?”
Cannabis-specific experience matters. A vendor familiar with METRC, state compliance requirements, and the industry’s unique challenges will serve you better.
The Questionnaire Template
Here’s a condensed questionnaire you can send to vendors:
VENDOR SECURITY QUESTIONNAIRE
Company Name: _________________
Service Provided: _________________
Contact: _________________
Date: _________________
CERTIFICATIONS
[ ] SOC 2 Type II (attach report)
[ ] SOC 2 Type I (attach report)
[ ] ISO 27001 (attach certificate)
[ ] Other: _________________
DATA HANDLING
1. What specific data do you require access to?
2. Where is data stored (geographic location)?
3. Is data encrypted at rest? (Algorithm: _________)
4. Is data encrypted in transit? (TLS version: ______)
5. How is our data segregated from other customers?
6. What is your data retention policy?
7. What is your data deletion process upon contract termination?
ACCESS CONTROLS
8. How many employees can access our data?
9. What roles have data access?
10. Is MFA required for all data access? [ ] Yes [ ] No
11. Describe your employee onboarding/offboarding procedures.
12. Are background checks conducted? [ ] Yes [ ] No
INCIDENT RESPONSE
13. What is your incident notification timeline? _____ hours
14. Attach or summarize your incident response plan.
15. Describe any security incidents in the past 3 years.
16. Do you carry cyber insurance? [ ] Yes [ ] No
Coverage limits: $_________________
SECURITY TESTING
17. When was your last penetration test? ___________
18. Can you share the executive summary? [ ] Yes [ ] No
19. What is your critical vulnerability patching timeline?
COMPLIANCE
20. CCPA/CPRA compliant? [ ] Yes [ ] No [ ] N/A
21. HIPAA compliant? [ ] Yes [ ] No [ ] N/A
22. Experience with cannabis industry? [ ] Yes [ ] No
REFERENCES
23. Provide 2-3 cannabis industry references.
Authorized Signature: _________________
Date: _________________
Red Flags to Watch For
During your vendor assessment, certain responses should trigger serious concern:
Immediate Disqualifiers
🚩 “We can’t share our SOC 2 report” - If they have one, they should share it under NDA. If they won’t, what are they hiding?
🚩 “We don’t require MFA for our employees” - This is basic security hygiene in 2026. No excuse.
🚩 “We’ve never had a security incident” - Either lying or not detecting incidents. Both are bad.
🚩 “We’ll notify you of breaches eventually” - Vague notification timelines mean you’ll be last to know.
🚩 “Our security is proprietary/secret” - Security through obscurity is not security.
Yellow Flags (Investigate Further)
⚠️ No SOC 2, but other documentation - Acceptable for small vendors, but require detailed security documentation.
⚠️ Recent security incidents - Not automatically disqualifying. How they handled it matters. Good incident response demonstrates maturity.
⚠️ Limited cannabis industry experience - May require additional education on compliance requirements.
⚠️ Offshore development or support - Not inherently bad, but understand where your data may be accessed from.
Contract Provisions That Protect You
Your vendor contract should include specific security provisions. Have your attorney ensure these are included:
Required Clauses
1. Security Standards
Vendor shall maintain security controls consistent with
industry standards, including but not limited to SOC 2
Type II certification or equivalent, and shall provide
annual evidence of compliance.
2. Breach Notification
Vendor shall notify Customer within twenty-four (24) hours
of discovering any actual or suspected security incident
affecting Customer data. Notification shall include:
nature of the incident, data affected, remediation steps,
and point of contact.
3. Audit Rights
Customer shall have the right, upon reasonable notice, to
audit Vendor's security controls or require Vendor to
provide third-party audit results. Audits may be conducted
annually and following any security incident.
4. Data Handling
Vendor shall: (a) encrypt all Customer data at rest and
in transit, (b) limit access to authorized personnel only,
(c) not share Customer data with third parties without
written consent, (d) return or destroy all Customer data
within thirty (30) days of contract termination.
5. Cyber Insurance
Vendor shall maintain cyber liability insurance with
minimum coverage of $[AMOUNT] and shall name Customer
as an additional insured for claims arising from
Vendor's security failures.
6. Indemnification
Vendor shall indemnify, defend, and hold harmless
Customer from any claims, damages, or losses arising
from Vendor's failure to maintain adequate security
controls or Vendor's breach of this agreement.
7. Subcontractor Requirements
Vendor shall ensure that any subcontractors or third
parties with access to Customer data maintain equivalent
security controls and are bound by equivalent
confidentiality obligations.
Ongoing Vendor Management
Assessment isn’t a one-time event. Your vendors’ security posture can change, and you need to monitor it.
Annual Review Cycle
Every Year:
- Request updated SOC 2 reports or security documentation
- Review any security incidents from the past year
- Reassess vendor tier classification
- Verify insurance coverage remains adequate
- Update vendor inventory
After Any Incident:
- Request detailed incident report
- Assess root cause and remediation
- Evaluate whether to continue relationship
- Update risk assessment
When Renewing Contracts:
- Renegotiate security provisions if needed
- Update data handling requirements
- Verify compliance with any new regulations
Vendor Risk Dashboard
Track your vendor security status:
Vendor Tier SOC 2 Last Review Insurance Issues
POS Provider 1 ✅ 2026-01 $5M None
Delivery Platform 1 ✅ 2025-11 $2M None
HVAC Service 3 N/A 2025-06 $1M None
Email Marketing 2 ⚠️ 2025-08 $1M SOC 2 pending
Vendor Security Monitoring
Beyond paperwork, consider active monitoring:
Dark Web Monitoring: Services can alert you if your vendors’ credentials appear in breach dumps. If your POS vendor’s admin credentials are on the dark web, you want to know.
News Monitoring: Set up Google Alerts for your critical vendors + “breach” or “hack”. You don’t want to learn about a vendor breach from Twitter.
Threat Intelligence: If you subscribe to cannabis industry threat intelligence (like Cannabis ISAO), watch for alerts about vendor targeting.
The Vendor Security Conversation
Talking to vendors about security can feel awkward. Here’s how to approach it:
For New Vendors
Frame it as due diligence:
“We’re very interested in your platform. Before we move forward, our compliance team requires us to conduct a security assessment of all vendors who handle customer data. Can you provide your SOC 2 report and complete our security questionnaire?”
Any legitimate vendor expects this. If they push back, that’s a red flag.
For Existing Vendors
Frame it as industry standard:
“As part of our annual compliance review, we’re updating our vendor security documentation. Can you provide your current SOC 2 report and answer a few questions about any changes to your security program since last year?”
When Vendors Don’t Meet Standards
Be direct but professional:
“Based on our assessment, we’ve identified some gaps between your current security posture and our requirements. Specifically: [list issues]. We’d like to understand your timeline for addressing these, as they’re required for us to continue the relationship.”
When to Walk Away
Sometimes the right answer is to find a new vendor. Consider termination when:
Hard Stops:
- They refuse to provide basic security documentation
- They’ve had a significant breach with poor response
- Their security posture has degraded substantially
- They can’t meet regulatory requirements (HIPAA, CCPA)
Negotiable If Addressed:
- Missing certifications but willing to obtain them
- Incident history but strong remediation
- Limited cannabis experience but willing to learn
- Contractual gaps they’re willing to fix
The Transition Plan: Before terminating a critical vendor, ensure you have:
- Alternative vendor identified and vetted
- Data migration plan
- Timeline that avoids operational disruption
- Written confirmation of data deletion from old vendor
Cannabis-Specific Vendor Considerations
Some vendor considerations are unique to cannabis:
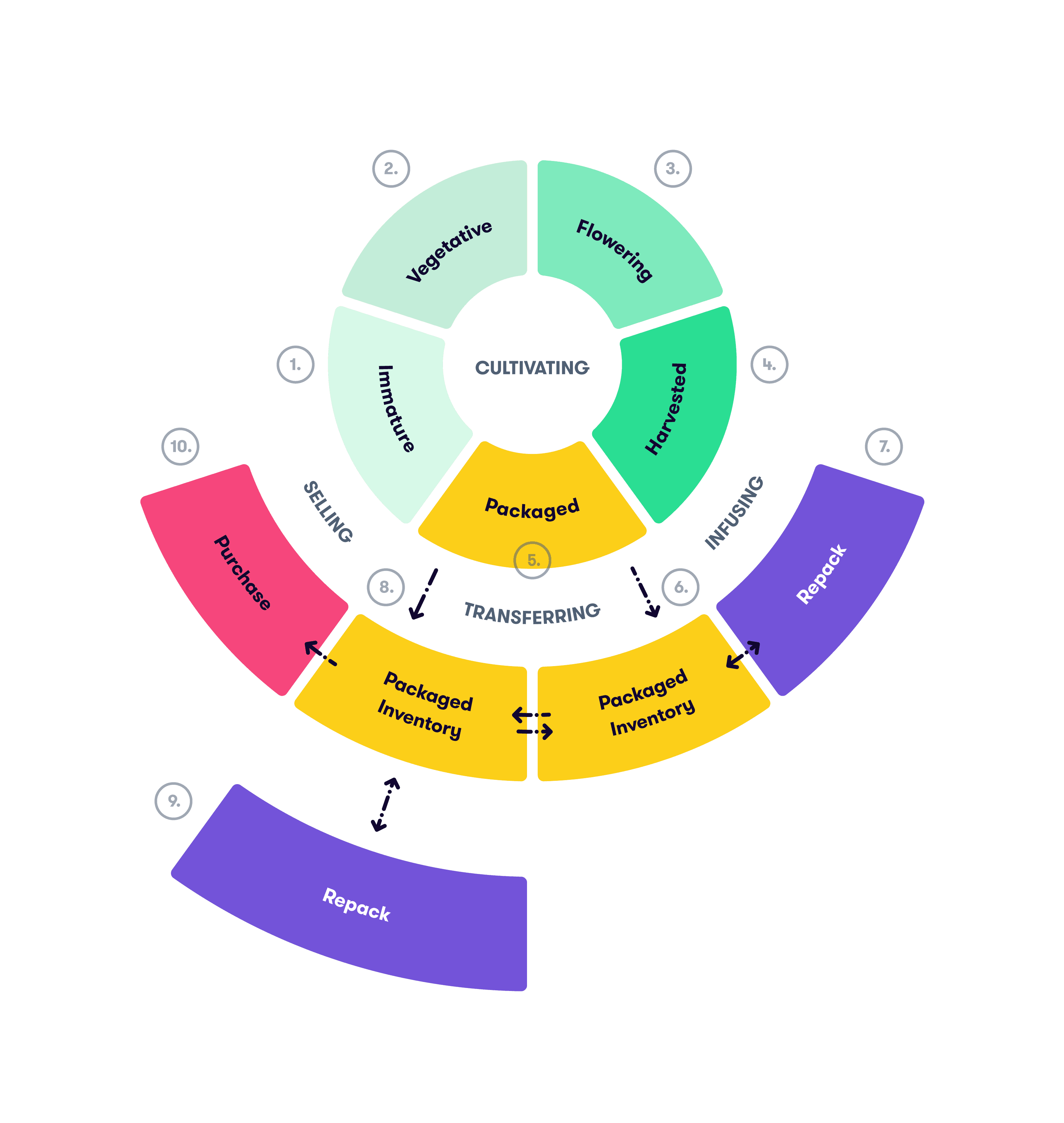
METRC Integration
If a vendor integrates with METRC, they need to understand:
- State-specific METRC rules
- Reporting requirements
- How to handle discrepancies
- That METRC data is effectively regulatory evidence
Cannabis Banking Limitations
Your payment processor needs to understand cannabis banking challenges:
- Cash handling procedures
- Cannabis-friendly banking relationships
- State-by-state payment restrictions
Regulatory Audit Support
Can your vendor provide data in formats required by state regulators? When the DCC asks for records, you don’t want to discover your vendor can’t export them properly.
280E Considerations
Does your accounting vendor understand 280E tax implications? Cannabis businesses face unique tax treatment that general accountants often mishandle.
Resources and Tools
Security Assessment Tools
- CAIQ (Consensus Assessments Initiative Questionnaire) - Cloud Security Alliance’s standard questionnaire
- SIG (Standardized Information Gathering) - Shared Assessments program questionnaire
- NIST Cybersecurity Framework - Reference for security control categories
Vendor Risk Platforms
- BitSight
- SecurityScorecard
- UpGuard
- Prevalent
Cannabis Industry Resources
- Cannabis ISAO - Threat intelligence for cannabis
- NCIA Compliance Resources - Industry association guidance
- State regulator websites - Vendor requirements by state
The Bottom Line
Your vendors are an extension of your security perimeter. Every integration, every data sharing agreement, every third-party access point is a potential path for attackers.
The STIIIZY breach should be a wake-up call for the entire industry. It doesn’t matter how strong your internal security is if your POS vendor gets compromised.
Start your vendor assessment today:
- Inventory all vendors with data access
- Categorize by risk tier
- Send security questionnaires to Tier 1 vendors
- Review and negotiate contracts
- Establish ongoing monitoring
Don’t be the next headline. Your customers trusted you with their data—and that trust extends to every vendor you let into your ecosystem.
CannaSecure helps cannabis businesses evaluate and manage vendor security risk. Contact us for vendor assessment templates and compliance guidance.